AI ROI: 2026 Benchmarks
Download Report
Money moves at the speed of light. A wire transfer crosses continents in seconds. Cryptocurrency changes hands in milliseconds. Funds can traverse a dozen jurisdictions before a compliance analyst finishes their morning coffee.
Yet most anti-money laundering (AML) programs operate on timelines measured in days or weeks. Batch processing runs overnight. They understand that alerts generated on Friday evening won't receive human attention until Monday morning at the earliest. They've mapped the investigation timelines at major financial institutions and designed their schemes to complete before meaningful intervention becomes possible.
Alert queues build up over weekends. Investigations stretch across months. By the time suspicious activity reaches human review, the funds have long since vanished into the legitimate financial system or been converted into assets that prove nearly impossible to trace.
This speed gap represents the fundamental structural disadvantage facing financial crime compliance. Criminal enterprises design their operations around velocity, knowing that every hour of delay between transaction and detection improves their odds of success. Traditional AML programs, built on manual processes and periodic reviews, simply cannot compete.
AML automation offers the only viable path to closing this gap. But achieving genuine real-time capability requires rethinking not just technology but the entire operational model that most institutions have built over decades.
AML and KYC flows are the most common use cases for predictive AI in financial services in 2025, as institutions seek to automate repetitive, rules-based compliance tasks and reduce errors that previously resulted in ~$24 billion in fines in 2024.

In 2025, over 266 billion real-time transactions were processed globally - a 63 % increase from the prior year - highlighting how quickly money moves and why AML systems must evolve beyond batch processing. The shift from batch to real-time processing represents more than a technical upgrade. It requires fundamentally different architecture and operational approaches.
Batch processing aggregates transactions over a period, typically 24 hours, then analyzes the complete dataset against detection rules. This approach made sense when computational resources were expensive and data integration was difficult. It allowed institutions to run complex analyses against complete daily activity without impacting production systems.
Continuous monitoring evaluates each transaction as it occurs. Rather than waiting to see the complete picture of daily activity, the system makes risk assessments in the moment, when intervention remains possible. A suspicious wire transfer can trigger an alert before the funds leave the institution rather than hours after they've reached their destination.
This immediacy changes what responses become feasible. With batch processing, even the fastest investigation begins after funds have moved. The institution can file regulatory reports and potentially assist law enforcement, but direct intervention in the criminal scheme isn't realistic.
Real-time detection opens different possibilities. Transactions can be held for review before execution when risk indicators exceed thresholds. Accounts can be restricted immediately upon detection of suspicious patterns. Relationship managers also receive instant notification when their clients engage in concerning activity.
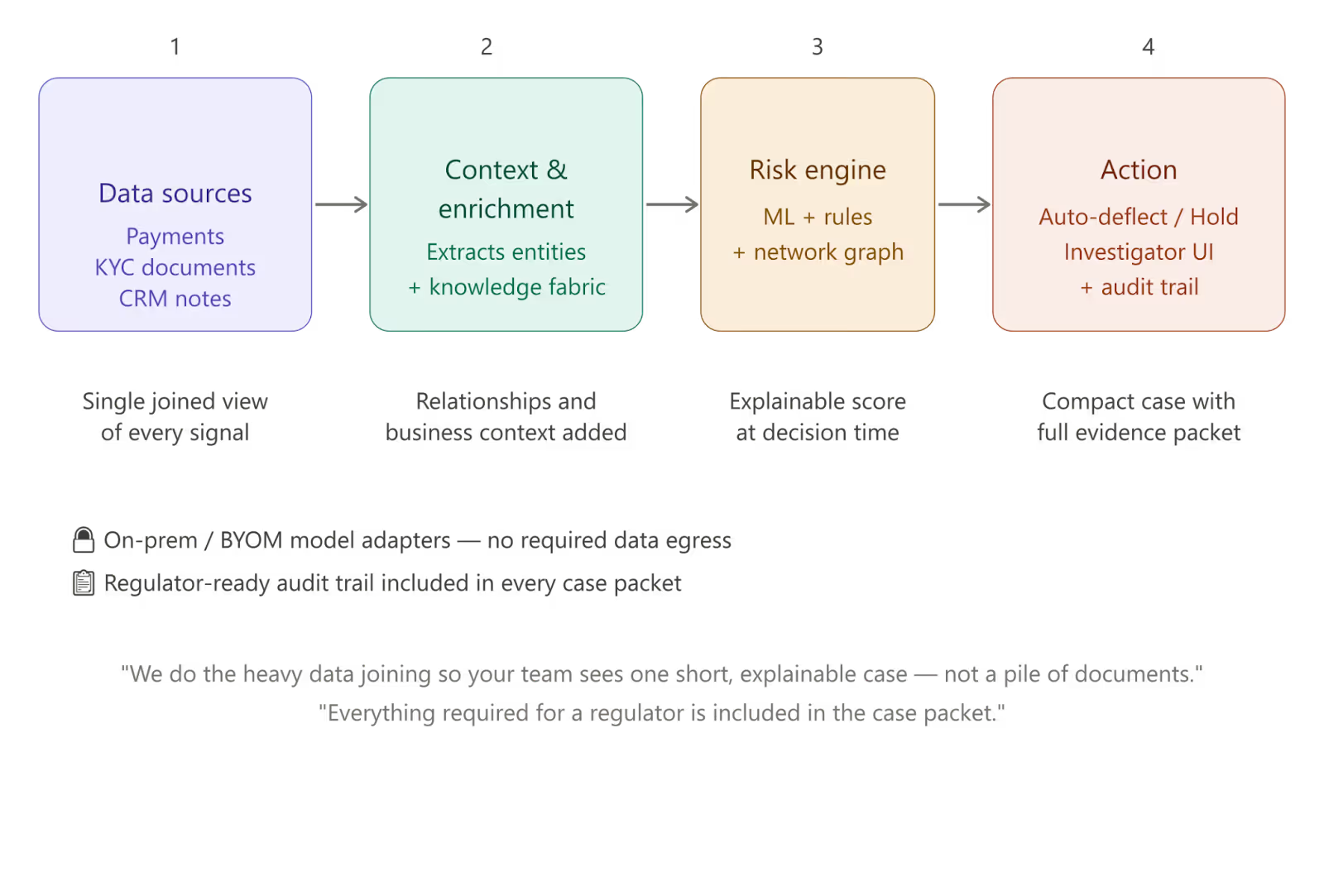
Instead of forcing investigators to piece together transactions, documents, and customer context manually, modern AML systems bring everything together into a single, explainable case.
Data from payments, KYC files, and customer interactions is unified and enriched with context - relationships, patterns, and historical signals. Risk is then assessed in real time using a combination of models, rules, and network analysis.
The result is immediate action. Low-risk cases are automatically resolved. High-risk activity is surfaced to investigators with all supporting evidence already assembled - transactions, relationships, and source documents - so decisions can be made quickly and confidently.
Every step is recorded with full traceability, ensuring that both internal teams and regulators can understand exactly how and why each decision was made.
While real-time monitoring addresses the detection delay, the most advanced AML automation goes further by predicting likely criminal behavior before transactions occur. This predictive capability emerges from pattern recognition across historical data.
Machine learning models trained on confirmed money laundering cases identify the precursor behaviors that typically precede illicit transactions. Account opening patterns associated with shell companies. Relationship networks that match known layering structures. Communication patterns between accounts that suggest coordination.
When these precursor signals appear, automation can flag accounts for enhanced scrutiny before any suspicious transaction occurs. Rather than reacting to money laundering after the fact, institutions can proactively focus investigative resources on the accounts and relationships most likely to present problems.
The effectiveness of predictive detection depends heavily on the breadth of data available for analysis. Models that only see transaction data miss signals visible in account opening documentation, customer communications, and relationship manager notes. Models that only see a single institution's data miss network patterns spanning multiple banks.
This creates a strong argument for integrated platforms that can incorporate diverse data sources and, where regulations and data sharing agreements permit, pool anonymized pattern information across institutions. Criminal networks operate across the financial system. Detection capabilities that stop at institutional boundaries will always be outmaneuvered.
Money laundering is fundamentally a network activity. Funds flow through webs of accounts, entities, and transactions designed to obscure connections between criminal proceeds and their ultimate beneficiaries. Understanding these networks is essential to effective detection.
Human analysts can trace networks, but the process is painfully slow. Following a chain of transactions across multiple accounts, documenting relationships, and identifying beneficial owners behind shell companies can consume weeks of investigative time.
Machine learning transforms network analysis from a bottleneck into a detection strength. Graph algorithms can trace relationship networks across millions of entities in seconds, identifying connection patterns that no human could spot manually.
This network visibility matters especially for detecting professional money laundering operations. Traditional transaction-level monitoring might flag individual transactions within these networks, but misses the larger pattern that reveals the operation's full scope.
Automation that surfaces network patterns allows investigators to address entire criminal infrastructures rather than individual transactions. A single investigation can identify and close all accounts associated with a laundering network, rather than playing endless whack-a-mole as funds shift between compromised accounts.
Speed in detection means nothing if the underlying data arrives slowly or incompletely. Many institutions discover that their automation ambitions are constrained not by analytical capabilities but by data infrastructure that introduces its own delays and gaps.
Transaction data flowing from core banking systems may be available only after end-of-day processing completes. Customer information residing in separate CRM platforms may not link cleanly to transaction records. Beneficial ownership data sitting in document management systems may require manual extraction before analysis.
Building genuine real-time AML capability requires treating data integration as foundational infrastructure rather than a secondary concern. Information must flow continuously from source systems to analytical platforms without batching delays. Data models must connect customer identities across products and business lines to enable complete relationship visibility. External data feeds from sanctions lists, adverse media sources, and beneficial ownership registries must update in near real-time.
The institutions that achieve fastest time-to-detection are typically those that invested in data connectivity platforms capable of bridging legacy systems with modern analytical infrastructure. They avoided the trap of attempting to replace all source systems before improving detection capabilities. Instead, they built integration layers that pull necessary information from existing systems while preserving those systems' core functions.
Financial regulators have encouraged adoption of advanced AML technology, but the regulatory framework itself still reflects batch-processing assumptions. Institutions implementing real-time AML automation should engage proactively with their regulators about evolving capabilities. Examiners generally respond positively to well-documented programs that demonstrate genuine improvement in detection and prevention, but they need to understand how real-time approaches differ from traditional models.
Particular attention should go to documenting decision-making authority and escalation procedures. When automation can trigger immediate transaction holds or account restrictions, regulators want assurance that appropriate governance surrounds these capabilities. Clear policies defining when automated intervention is appropriate, what human oversight applies, and how exceptions are handled all become essential.
Financial institutions that achieve real-time AML capabilities find that speed advantages compound over time. Faster detection means investigators work with fresher information. Quicker case resolution also frees investigative capacity for proactive work. Rather than perpetually fighting backlogs, analysts can pursue complex cases, develop typology expertise, and contribute to continuous improvement of detection models.
These compounding advantages widen the gap between institutions that achieve real-time capabilities and those that continue operating in batch mode. The leaders get progressively stronger while the laggards face increasing concentration of criminal activity seeking the path of least resistance.
The question facing every financial institution is which side of that divide they want to occupy. We’d love to help you get on the right side of the conversation, just book a meeting.

Tell us the use case. We'll show you what's possible - live, on your data, in days.